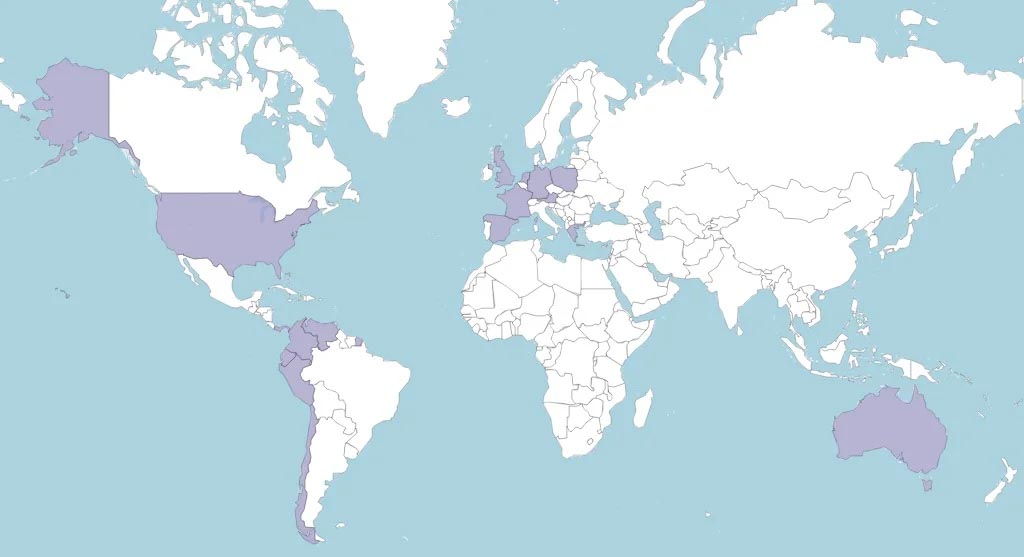
For almost two years, from June 2021 to April 2023, a widespread eCrime campaign targeted clients of prominent banks worldwide. The mastermind behind this operation, known as Neo_Net, focused primarily on Spanish and Chilean banks, successfully compromising the security of several financial institutions. Security researcher Pol Thill’s finding published by SentinelOne sheds light on the operations of Neo_Net and his Smishing-as-a-Service platform called Ankarex.
The Campaign:
Neo_Net employed a sophisticated multi-stage attack strategy, starting with SMS phishing messages sent across Spain using his proprietary service called Ankarex. These messages imitated reputable financial institutions, tricking victims into clicking on malicious links. The phishing pages used by Neo_Net were carefully designed to resemble genuine banking applications, employing defense measures to evade detection. Once victims submitted their credentials, the information was surreptitiously exfiltrated to a Telegram chat, granting the threat actors unrestricted access to stolen data.
Circumventing Multi-Factor Authentication (MFA):
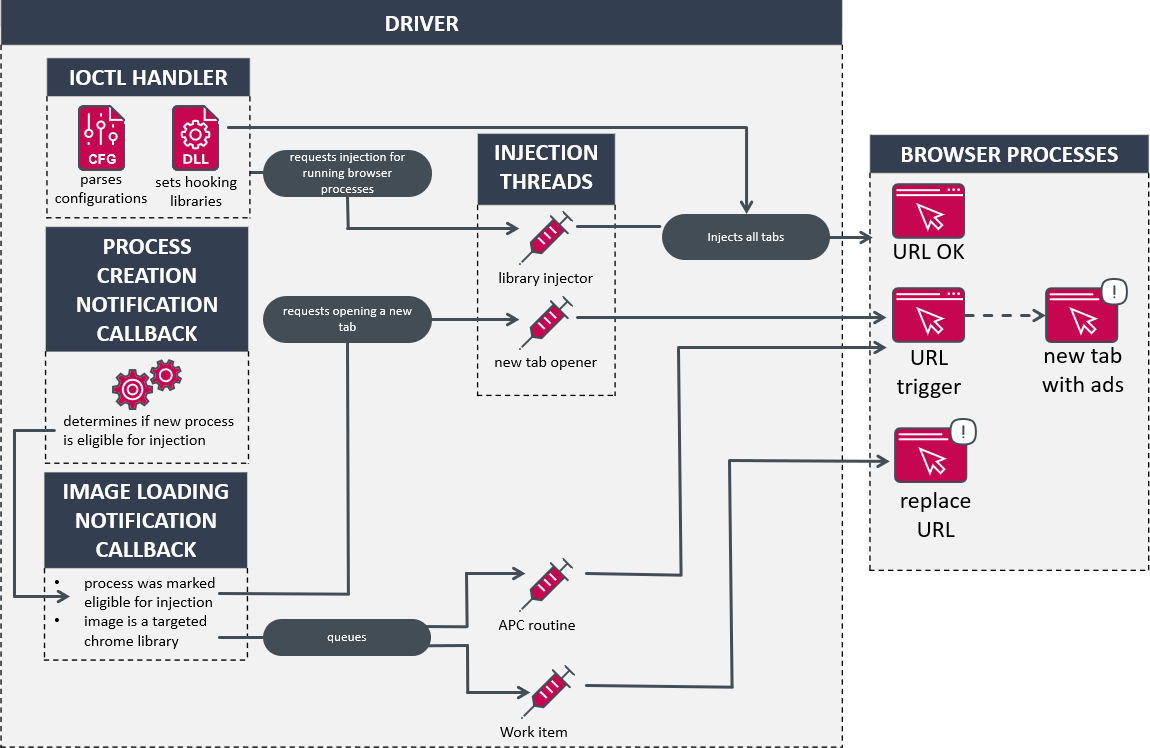
Neo_Net coerced victims into installing a purported security application on their Android devices to bypass MFA mechanisms commonly used by banking applications. These applications, which were trojans disguised as security tools, gained permission to view and send SMS messages. The threat actors could circumvent MFA by covertly exfiltrating incoming SMS messages, including One-Time Passwords (OTPs). Direct phone calls to victims were also used to deceive them into installing Android spyware or disclosing OTPs.
The Success and Impact:
Despite using relatively unsophisticated tools, Neo_Net, and its affiliates stole over 350,000 EUR from victims’ bank accounts and compromised a significant amount of personally identifiable information (PII). Their success can be attributed to the highly targeted nature of their operations, focusing on specific banks and meticulously copying their communications to impersonate bank agents. The simplicity of SMS spyware made detecting it challenging, as it only required permission to send and view SMS messages.
Neo_Net’s Background and Ankarex:
Neo_Net, the Mexico-based hacker behind the global cybercrime campaign, has been active since early 2021. He founded Ankarex, a Smishing-as-a-Service platform that enables infrastructure rental to multiple affiliates. Through Ankarex, Neo_Net offered leads and advertised his Android SMS spyware service. He collaborated with individuals from a Spanish-language IT forum and was traced back to several unique IP addresses in Mexico.
Conclusion:
Neo_Net’s eCrime campaign targeting banks showcased the significant damage even unsophisticated cybercriminals can cause. The campaign’s success was attributed to highly targeted operations, impersonating bank agents, and exploiting the vulnerability of SMS-based multi-factor authentication. This highlights the need for more robust safeguards like physical tokens or external applications to enhance security. The impact of Neo_Net’s operation underscores the importance of continuous vigilance and strong cybersecurity measures for financial institutions and individuals alike.